BankrBot and the Wild West of Crypto Trading Skills
The promise is intoxicating: plug a crypto trading skill into your AI agent and let it trade autonomously across exchanges, prediction markets, and DeFi protocols. BankrBot has emerged as the leading library making this promise real — and its rapid growth tells a story about both the potential and the peril of open skill ecosystems.
What BankrBot Offers
BankrBot is a curated library of crypto-focused skills designed specifically for AI agents. The collection spans the full spectrum of crypto trading operations:
- •Polymarket Skills — automated trading on prediction markets, including liquidity provision, arbitrage detection, and event-driven strategies
- •Exchange Connectors — unified interfaces to major centralized exchanges like Binance, Coinbase, and Kraken, handling authentication, order placement, and portfolio tracking
- •DeFi Interactions — skills for interacting with decentralized protocols, including token swaps, yield farming, and liquidity pool management
- •Analytics Tools — market data aggregation, sentiment analysis, and on-chain metrics for informed decision-making
For developers building trading agents, BankrBot dramatically reduces time-to-market. Instead of writing exchange API integrations from scratch, you install a skill and start trading.
The Appeal of Autonomous Trading
The crypto market never sleeps, and neither do AI agents. This fundamental alignment has driven explosive interest in autonomous trading bots. A well-configured agent can monitor hundreds of markets simultaneously, execute trades in milliseconds, and adjust strategies based on real-time data — all without human fatigue or emotional bias.
BankrBot skills integrate seamlessly with OpenClaw's agent framework. A developer can chain together market analysis, execution, and risk management skills to create sophisticated trading systems that operate around the clock. The composability of the skill architecture means strategies can be assembled modularly, tested in simulation, and deployed incrementally.
The Dark Side
In early 2026, security firm Snyk published findings that sent shockwaves through the community: they had identified 386 malicious skills published to the BankrBot registry. These were not buggy or poorly written skills — they were deliberately crafted to exploit users.
The attack vectors were varied and sophisticated:
- •Credential Harvesting — skills that captured API keys, private keys, and authentication tokens during normal operation, silently exfiltrating them to attacker-controlled servers
- •Transaction Redirection — skills that subtly modified transaction parameters, redirecting small percentages of trades to attacker wallets in ways that were difficult to detect in high-volume trading
- •Wallet Draining — skills that, once granted wallet permissions, executed unauthorized transfers during periods of low monitoring
- •Dependency Poisoning — skills that appeared legitimate but pulled in malicious sub-dependencies that compromised the entire agent environment
Many of these malicious skills had convincing names, documentation, and even fake download statistics. Some mimicked popular legitimate skills with slight name variations — a classic typosquatting attack adapted for the skill ecosystem.
The Ecosystem Trust Challenge
The BankrBot situation highlights a fundamental tension in open skill ecosystems. The same openness that enables rapid innovation also enables rapid exploitation. When anyone can publish a skill, and skills have access to sensitive resources like API keys and wallets, the attack surface is enormous.
Traditional package managers like npm and PyPI have faced similar challenges, but the stakes in crypto are uniquely high. A malicious npm package might steal environment variables. A malicious trading skill can drain a wallet in seconds, and blockchain transactions are irreversible.
Security Recommendations
The community has converged on several critical practices for anyone using crypto trading skills:
- •Verified Publishers Only — prefer skills from verified, established publishers with track records and reputations to protect
- •Audit the Code — before granting any skill access to wallets or exchange accounts, review the source code thoroughly, paying special attention to network calls and transaction construction
- •Sandboxed Wallets — never connect a trading skill to your main wallet; use dedicated wallets with limited funds for testing and operation
- •Permission Minimization — grant skills only the specific permissions they need; a market data skill should not need withdrawal permissions
- •Monitor Transactions — set up independent monitoring for all wallet and exchange activity, with alerts for unexpected transactions
- •Regular Audits — periodically review installed skills for updates, known vulnerabilities, and suspicious behavior changes
The Broader Lesson
BankrBot's malicious skill problem is not unique to crypto — it is a preview of challenges every skill ecosystem will face as AI agents become more capable and more autonomous. When agents can take real-world actions with real financial consequences, the security of the skill supply chain becomes critical infrastructure.
The lesson is clear: security must keep pace with capability. Every new skill that gives agents more power also creates new attack surfaces. The ecosystem's long-term viability depends on building trust mechanisms that are as sophisticated as the skills themselves.
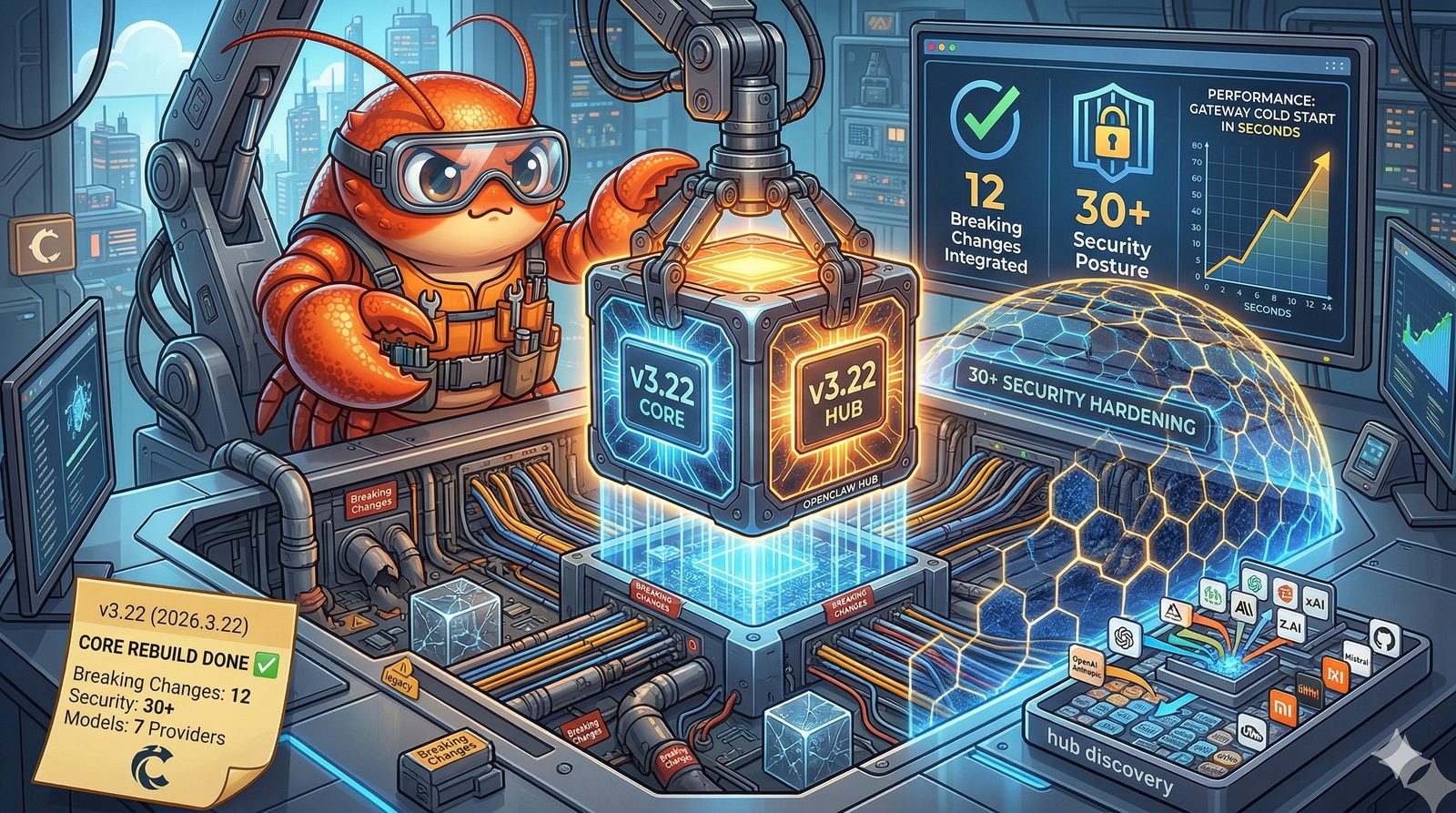
The OpenClaw Community Response
The OpenClaw community has responded to the BankrBot findings with concrete action:
- •A skill verification program that reviews and certifies skills from trusted publishers
- •Automated scanning tools that analyze skills for known malicious patterns before installation
- •A community reporting system for flagging suspicious skills, with rapid response teams for investigation and removal
The wild west of crypto trading skills is slowly getting its sheriffs. But in the meantime, every agent builder working with financial skills needs to be their own security team. Trust, but verify — and keep your private keys close.