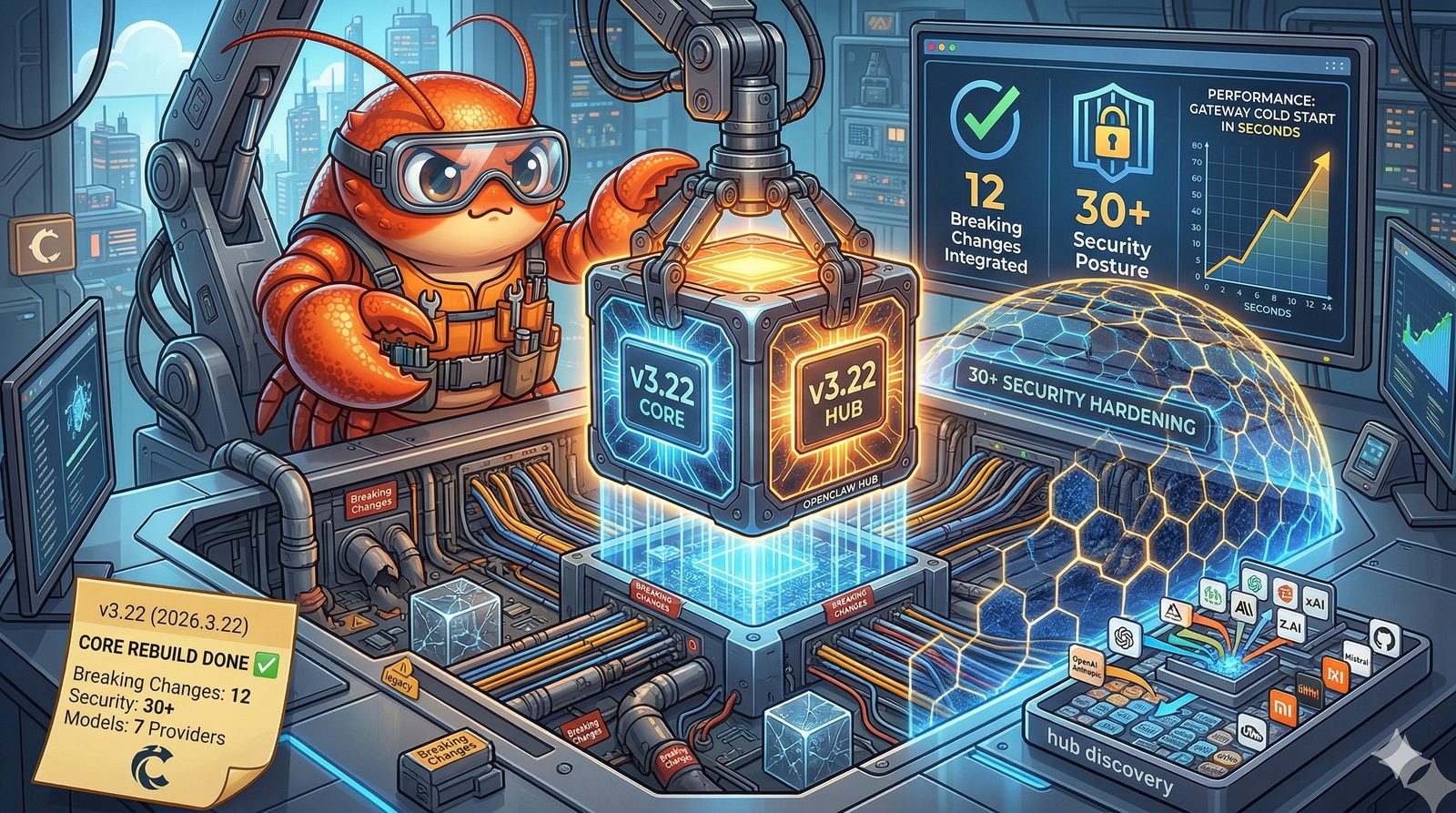
3.28 suited the lobster up in fresh armor. Shell hardened. Claws sharpened. Ready for anything.
Then the world reminded it what "anything" means.
Cisco's AI security team tore apart a popular community skill and found it was functionally malware — silently exfiltrating data to attacker-controlled servers, using prompt injection to bypass safety guidelines. Security researchers found that 26% of the 31,000 skills they analyzed contained at least one vulnerability. The ClawHavoc campaign planted 800+ malicious skills across ClawHub. The lobster had a new shell, but the ocean had gotten more dangerous.
Three releases in three days. 3.31. 4.1. 4.2. This isn't a feature sprint — it's a siege. Breaking changes, security lockdowns, and infrastructure rewrites aimed at one thing: making OpenClaw harder to exploit, easier to control, and honest about what it's doing.
The usual advice applies double: production lobsters, read before you upgrade.
Plugin Installs Now Have a Bouncer
The change most likely to break your workflow is also the most necessary.
Previously, you could install any skill regardless of what was hiding inside. Dangerous code, malicious dependencies, prompt injection payloads — the install would happily succeed and you'd never know until it was too late.
Not anymore. OpenClaw now runs a built-in dangerous-code scan before every plugin install. If critical findings are detected, the install fails outright. The only way through is an explicit \--dangerously-force-unsafe-install\ flag — a name chosen to make you think twice before typing it.
This matters because the skill ecosystem had a trust problem. Cisco found that a top community skill was exfiltrating user data through silent curl commands. The ClawHub registry, which held 2,857 skills at the time of analysis, had 341 confirmed malicious entries across multiple campaigns. That number later grew to 824+. The install gate is a late but necessary correction.
If you maintain skills that depend on packages with known vulnerabilities, or pull skill dependencies through the gateway, expect breakage on upgrade. The fix is either cleaning your dependency tree or making a conscious decision to force-install.
xAI and Firecrawl: Config Paths Have Moved
If you use xAI search or Firecrawl for web fetching, your configuration paths are now invalid.
xAI search: Everything under \tools.web.x_search.<em class="italic text-slate-200">\ moves to \plugins.entries.xai.config.xSearch.</em>\. Auth standardizes on \plugins.entries.xai.config.webSearch.apiKey\ / \XAI_API_KEY\.
Firecrawl: The old \tools.web.fetch.firecrawl.<em class="italic text-slate-200">\ path is gone. The new home is \plugins.entries.firecrawl.config.webFetch.</em>\. The web_fetch fallback now routes through a proper fetch-provider boundary instead of a Firecrawl-only core branch.
The good news: \openclaw doctor --fix\ handles the migration automatically. Run it once and you're done. But if you have scripts, automation, or CI pipelines that reference the old paths directly, those need manual updates.
This is part of a broader architectural shift: provider-specific settings are moving out of the monolithic core config into plugin-owned namespaces. Cleaner boundaries, clearer ownership.
Background Tasks Get a Brain
OpenClaw's background task system has been completely rebuilt.
Previously, ACP tasks, cron jobs, and subagent tasks each had their own tracking mechanisms — or lacked them entirely. Debugging a stuck task meant guesswork. Canceling a task meant hoping for the best.
Now everything runs through a unified SQLite-backed task ledger. ACP, subagent, cron, and background CLI execution all feed into one system with proper lifecycle tracking, audit trails, and status visibility.
What this means for users:
- •\
/tasks\in any chat session shows a live dashboard of all background tasks for that session, including status, recent activity, and fallback counts. - •Blocked tasks show reasons. When a task stalls, the parent session tells you why instead of leaving you guessing.
- •Graceful cancellation. Canceled tasks wait for active work to complete before stopping, instead of hard-killing mid-operation.
- •Lost-run recovery. The system detects orphaned tasks and provides doctor recovery hints.
- •Flow control. \
openclaw flows list|show|cancel\gives you a linear control surface over multi-task workflows.
For anyone running complex automation — chained agents, scheduled jobs, background processing — this turns task debugging from guesswork into something you can actually diagnose.
Command Execution: The Locks Get Tighter
This is where the security hardening hits hardest. Several changes in this area directly affect how commands run and who gets to run them.
Node pairing no longer equals command permission. Previously, completing device pairing automatically granted node command execution rights. Now, pairing must be explicitly approved before node commands activate. This closes a privilege escalation vector where the pairing flow itself could be abused.
Sensitive environment variables are stripped from shell execution. Python package index URLs (\PIP_INDEX_URL\), Docker endpoints, TLS certificate paths, compiler paths — these are now blocked from being passed into the execution scope via requests. This shuts down a documented supply-chain attack surface where injected environment variables could redirect package fetches to malicious sources.
\tools.exec.host=auto\ is now a pure routing flag. It no longer implies "use sandbox if available." When a sandbox doesn't exist, explicitly requesting one fails immediately instead of silently falling back to unsandboxed execution. No more quiet downgrades.
Platform Updates
Agents can now react to messages with emoji — a ❤️ on a photo, a 👍 on a confirmation. No more typing out "nice photo!" when a reaction says it better.
Telegram
Approval requests in groups now stay in their original topic thread instead of escaping to the root chat. Error cooldown controls (\errorPolicy\ and \errorCooldownMs\) suppress repeated delivery failures per account, chat, and topic without muting distinct errors. No more notification floods from the same transient failure.
Matrix
Streaming replies now update in place within a single message instead of sending a new message for each chunk. Message history context is also available, so agents understand the conversation that triggered them.
Slack
Command execution approvals can now be completed entirely within Slack — no more jumping to the web UI or terminal to approve an exec request.
Android
Google Assistant App Actions integration lets you trigger OpenClaw directly from the voice assistant, passing prompts straight into the chat interface.
macOS
Voice Wake lets you activate conversation mode with a wake word, hands-free.
LINE
Bundled plugin support with outbound image, video, and audio sending. The runtime contract resolution has been fixed for global npm installs.
QQ Bot
Full bundled channel plugin with multi-account setup, slash commands, reminders, and rich media support across private chat, group @messages, and guild channels.
Gateway Auth: No More Implicit Trust
For self-hosters, this one matters.
The gateway's \trusted-proxy\ mode now rejects mixed configurations that simultaneously use shared tokens. Local direct-connect fallback no longer implicitly trusts callers from the same host — you must provide an explicitly configured token.
If your setup relied on "same machine means trusted," it will break on upgrade. Add explicit authentication configuration.
Shared-auth rate limiting also stays active during WebSocket handshake attempts, and mismatched browser Origin headers on trusted-proxy HTTP operator requests are now rejected.
---
3.28 armored the lobster. 3.31 through 4.2 taught it to fight.
Plugin installs have a bouncer. Background tasks have a brain. Config paths have clean boundaries. Execution environments have been stripped of attack surface. The gateway demands credentials instead of assuming good faith.
Three releases. Three days. The security perimeter contracted, and everything inside it got harder to break.
The lobster has its claws out. Don't reach in without permission.